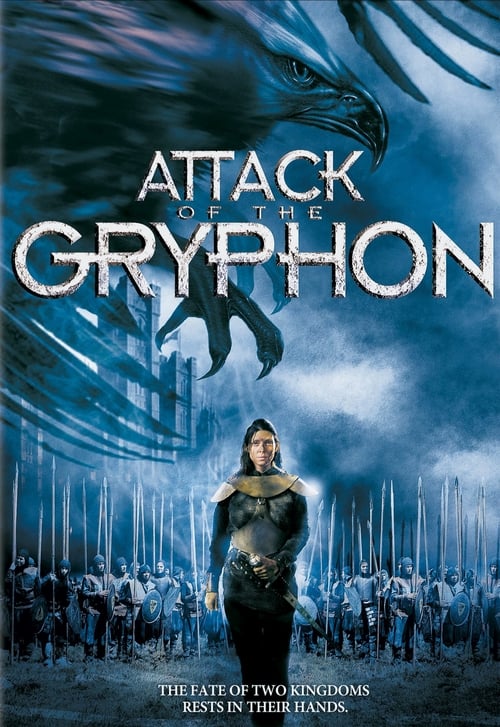
Free Watch Now Attack of the Gryphon (2007) Movie uTorrent Blu-ray Online Stream

Attack of the Gryphon Movies Solarmovie HD Without Download Streaming Online
Plot Attack of the Gryphon (2007):
In a mystical land torn apart by civil war, a warrior princess must team up with a rival warrior prince to hunt down an evil sorcerer who has summoned a giant flying demon which is terrorizing their land.Casts of Attack of the Gryphon:
Jonathan LaPaglia, Larry Drake, Amber Benson, Andrew Pleavin, Douglas Roberts, Ashley Artus, Sarah Douglas, Amy Gillespie, Simona Williams, Adrian PinteaMovie Side
Title: Attack of the Gryphon- Released: 2007-01-27
- Genre: Adventure, Fantasy, Action, Science Fiction
- Date: 2007-01-27
- Runtime: 89 Minutes
- Company: Nu Image, Media Pro Pictures
- Language: English
- Budget:
- Revenue:
- Plot Keyword : Adventure, Fantasy, Action, Science Fiction
- Homepage:
- Trailer: Watch Trailer
- Director: Boaz Davidson, Avi Lerner, John Thompson, Viorel Sergovici, Ioana Corciova, Trevor Short, Danny Dimbort, Andrew Prowse, Andrew Prowse, Amy Krell
Learn More About Attack of the Gryphon
Amber Benson looks good, and the Gryphon looks so bad that it's hilarious. Otherwise, a bland plethora of "meh"._Final rating:★½: - Boring/disappointing. Avoid if possible_
Cyber security how to use graphs to do an attack ~ Attack analysis with graph technologies As a cyber security provider Cisco keeps track of the domain names Through its data collection program Cisco has good information on 25 to 30 million Internet domains It knows which of these millions of domains are controlled by hackers and which are not
PDF Automated Generation and Analysis of Attack Graphs ~ An integral part of modeling the global view of network security is constructing attack graphs Manual attack graph construction is tedious errorprone and impractical for attack graphs
Bayesian attack graphs for platform virtualized ~ Bayesian attack graphs BAG are models that employ Bayesian networks to depict the security attack scenarios in an infrastructure or a system Extending the notion of Bayesian networks the nodes in a BAG can be used to represent system components that are vulnerable to attacks
What is Attack Graphs IGI Global ~ What is Attack Graphs 1 These are data structures that model all possible avenues of attack ing a network Two versions have been widely used 1 The first one is a direct graph where nodes represent network states and edges represent the application of an exploit that transforms one network state into another more compromised network state
What is Attack Graph IGI Global ~ Definition of Attack Graph A graph based structure representing the state of the system as vertices and actions such as vulnerabilities or normal system transitions which can change the state of the system as edges Attack graphs are similar to finite state machine diagrams that focus on security rather than system state
A taxonomy for attack graph generation and usage in ~ Attack graph generation is a process that includes vulnerability information processing collecting network topology and application information determining reachability conditions among network hosts and applying the core graph building algorithm
Efficient Defense DecisionMaking Approach for Multistep ~ The purpose of the attack graph 1 – 5 is to analyze the attackdefense actions of the network through nodes and edges in the graph Attribute attack graph regards the condition or attribute of the network as a node in the attack graph When studying network security it can accurately depict an event as a node in the network
GitHub ChandlerBangawesomegraphattackpapers ~ Adversarial Attacks on Neural Networks for Graph Data Daniel Zügner Amir Akbarnejad Stephan Günnemann KDD 2018 22 Untargeted Attack Backdoor Attacks to Graph Neural Networks Zaixi Zhang Jinyuan Jia Binghui Wang Neil Zhenqiang Gong arxiv 2020 paper Practical Adversarial Attacks on Graph Neural Networks
BigData Architecture for Cyber Attack Graphs ~ Attack graph represented as property graph This explicitly encodes the domain membership that is implicit in Cauldron An advantage of the protection domain abstraction is that the number of edges among machines in a domain is linear in the number of machines rather than quadratic
Digital Attack Map ~ Shows attacks on countries experiencing unusually high attack traffic for a given day Combined Shows both large and unusual attacks Copy this code into your page dismiss Attack Bandwidth Gbps Dates are shown in GMT Data shown represents the top 2 of reported attacks


0 Comments